Cyber Security Benefits: Accelerating Business Growth and More
Last update: 19 May 2026 at 03:50 pm
Cyber security benefits impact businesses of all sizes, reshaping operations in our interconnected world. In a digitally interconnected world human-machine interactions undergo seismic changes.
There’s no denying that such interaction has brought several technological benefits to companies thanks to super-fast computing and other spoils. Unfortunately, the world has also encountered many potential threats surrounding cyber security, hacking, malicious cyber attacks, and data breaches.
Cybersecurity threats jeopardize data, finance, and reputation, demanding urgent protection for businesses. Therefore, businesses must make stealthy internet cyber security their number one objective.
Security Systems: A growth enabler
Cyber security, beyond defense, unlocks opportunities as a catalyst for business growth.
You read it right: cyber security is a business growth enabler!
This means that any business not focusing on cybersecurity solutions is missing out on significant opportunities for innovating and growing.
So, what are companies doing to ensure they’re embracing cyber security with an eye on innovation and growth?
Data Security: Securing Customer Data
Collecting customers’ contact information is likely (and should be) a part of your marketing strategy. Without this step, you may as well throw in the towel.
To grow your business, you’ll likely want to utilize channels like PPC or social media to drive traffic to landing pages you’ve created on your website to build your pipeline or email lists. On these pages, you’ll have lead magnets set up to entice your site visitors to give up their contact info in exchange for something free.
Collecting data with lead magnets
Your content team will create these things, like eBooks, white papers, demo videos, free trials, coupon codes, free templates like accounting templates, and other giveaways that add value for the reader. And while this is an excellent way to build your pipeline and increase lead generation, it also gives you access to customer data like email addresses, phone numbers, bank account details, and other data your target audience likely wants to keep private. In many cases, organizations work with cloud security experts to strengthen protection strategies and reduce potential vulnerabilities.
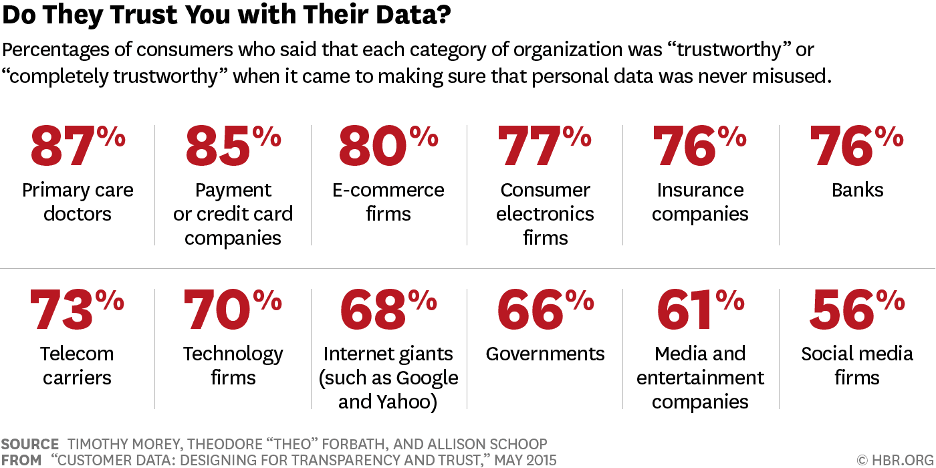
Most people have difficulty giving away their info, as it requires a certain level of trust. So, suppose you request more personal information from your target audience to download the free benefits of the promotional offer you’re giving away. In that case, you need to take steps for data security.
Empowering Mobile Employees
Things are evolving fast, and companies are following suit! Initially, most of a company’s cyber security focus would be given to PCs in an office setting.
However, with the current increased mobility of the workforce due to remote working, focusing only on the security of the PCs in your office is a waste of time as much as necessary.
Most companies are now looking to increase their levels of productivity as well as geographically expand their workforce. Therefore, their focus is now on empowering the mobile workforce.
While it’s not an easy task to accomplish the process when everything is in place with a company’s mobile infrastructure, it’s a breeze to avert data breaches and security risks while enabling innovation, accelerating growth, and opening up your business to recruit top talent from across the globe. Additionally, collaborating with branding agencies in Dubai can enhance your branding efforts to attract a larger, diverse talent pool.
Protecting Critical Assets
Protecting a business’s critical assets is a no-brainer, especially in the current digital-centric world. In fact, from the experience of companies that have been targeted, after the incident, most of the businesses are unable to come back to life again, or it may take a long period to rediscover their form and regain their footing.
Ways to protect your assets
There are several means that a business can use to ensure that they protect their critical assets. For instance, they can use multi-factor authentication, user and device certificate provision, role-based access control, mobile device management, enterprise, cloud identity management, single sign-on (SSO), and privileged user management. These can each come into play, depending on your circumstance.
Such strong protection does much more than provide network security for users. Business operations with improved cybersecurity measures have enhanced customer loyalty and trust.
Many of a company’s assets are related to customers’ personal information, making them even more critical to protect. That way, the company enhances its reputation in the market, which helps to attract new customers. To state the obvious, more customers with a higher level of trust = more business and increase brand authority.
Streamlining Compliance
It can be overwhelming for a company to comply with government and data privacy regulations. In fact, for most companies, the process might hinder the growth and expansion of the business as everything focuses on avoiding risks rather than taking them (taking risks can be hugely valuable for companies in the right situation).
Everything has to be done while keeping a sturdy security posture intact. Moreover, it becomes even more challenging for a company to keep up with evolving cyber threats and protective standards.
Therefore, since technology is moving, it’s essential to streamline the compliance sector to ensure companies focus on their growth by merely innovating new offerings and extending their business reach.
Successful companies are those that conduct risk analysis, deploy the correct security technology, develop policies and procedures, deploy a cloud, and then test the solutions to ensure they are compliant.
Risk is excellent, but the best bet is calculated risk. And it would be best if you never took risks regarding cyber security.
Embracing Cloud
Most organizations are shifting to the Cloud to support the business and mobile workers. It’s arguably the best modern means of enabling more robust and seamless collaboration.
And collaboration is critical in today’s interconnected business world. Whether collaborating with your team on a project, tracking business results through your CRM, or sharing sensitive files with a partner organization, business is shifting more and more to operations in the Cloud. You’re putting your business behind if you aren’t set up to operate securely in the Cloud.
Value of hosted cloud environments
Unlike the on-premises solutions available, Hosted cloud environments offer great benefits for employee collaboration and easy access to susceptible data from almost anywhere. This greater accessibility can help your company to innovate and grow.
Furthermore, modernizing the IT infrastructure and migrating into the Cloud comes with savings; given that a company doesn’t have to maintain or continually update the IT sector, that’s usually the case for the on-premises environment.
If you avoid the overhead of taking on all these operations in-house, you can realize some serious savings to pile on to the enormous benefits available.
The Inter-link
In conclusion, cyber security and the growth of a business are interlinked.
However, it’s unfortunate that most companies are yet to uncover the correlation.
But the need to see cyber security from another angle will become more apparent sooner than later. For now, those companies that prioritize cyber security are reaping their benefits as an enabler for innovation and growth.
You’re falling behind if your company doesn’t fall into the “ahead of the game” category regarding cyber security. The digital world changes too fast to sit idly by and fail to consider the implications of not being on top of what we’ve discussed today in this article.
So, sit down with your leadership team and discuss the benefits and logistics of implementing enhanced cybersecurity procedures within your organization. Whether looking at your website, social media, your CRM, or any other customer touchpoint or place you save more data, ensure you do it safely.
Don’t let cyber security slip off your plate because it isn’t public-facing and not as exciting as video marketing, speaking engagements, and other public stuff you do to grow your business. Trust me, if you do cyber security incorrectly, it will become public-facing, and you don’t want that.
So, get your cyber security to ensure your business continues to grow and doesn’t fall victim to a PR nightmare. Do it today before you are digitally light years behind the competition.
Author Bio
Anthony is the Founder of AnthonyGaenzle.com and the author of Blogging for Business: Skyrocket Your Traffic, Grow Your Readership, and Boost Revenue. Beyond running the publication, Anthony works with small businesses, startups, and creative minds to help you grow. Throughout his 15+ years in marketing and multimedia, he has worked with companies across various industries and disciplines, achieving significant growth in brand awareness, lead generation, revenue, and other critical areas. He also helps individuals build influence and thought leadership through powerful personal branding. Follow Anthony on Twitter or connect on LinkedIn.